CRYPTO
Hellman Key: The Cryptographic Breakthrough Behind Secure Internet Communication
Every time you log into online banking, send a WhatsApp message, or connect to a VPN, a silent mathematical process happens in the background. Two devices, often strangers to each other, create a shared secret over a public network without ever directly sending that secret across the internet.
That breakthrough is commonly referred to as the Hellman key exchange, more accurately known as the Diffie–Hellman key exchange.
Today, this concept underpins HTTPS, TLS, SSH, VPN tunnels, encrypted messaging apps, cloud infrastructure, and even blockchain security models.
Table of Contents
What Is the Hellman Key Exchange?
The Hellman key exchange is a cryptographic protocol that allows two parties to generate a shared secret key while communicating over a public network.
The system was developed by Whitfield Diffie and Martin Hellman, which is why the protocol is formally called the Diffie–Hellman Key Exchange (DHKE).
The revolutionary idea was simple but powerful:
- Two users can agree on a secret encryption key
- Without previously sharing any secret information
- Even if attackers can observe all network traffic
That concept became the foundation of public-key cryptography.
Why the Hellman Key Changed Cybersecurity Forever
Before Diffie–Hellman, cryptography relied mainly on symmetric encryption.
In symmetric systems:
- The same key encrypts and decrypts data
- Both parties must already know the secret key
This created a massive “key distribution problem.”
Imagine:
- A bank with 10 million customers
- Every customer needs a unique secure key
- Keys needing safe physical delivery
The logistics were nearly impossible.
The Hellman key exchange solved this by enabling:
- Secure key creation online
- No prior trust relationship
- Scalable internet encryption
Without it, the modern web would not exist in its current form.
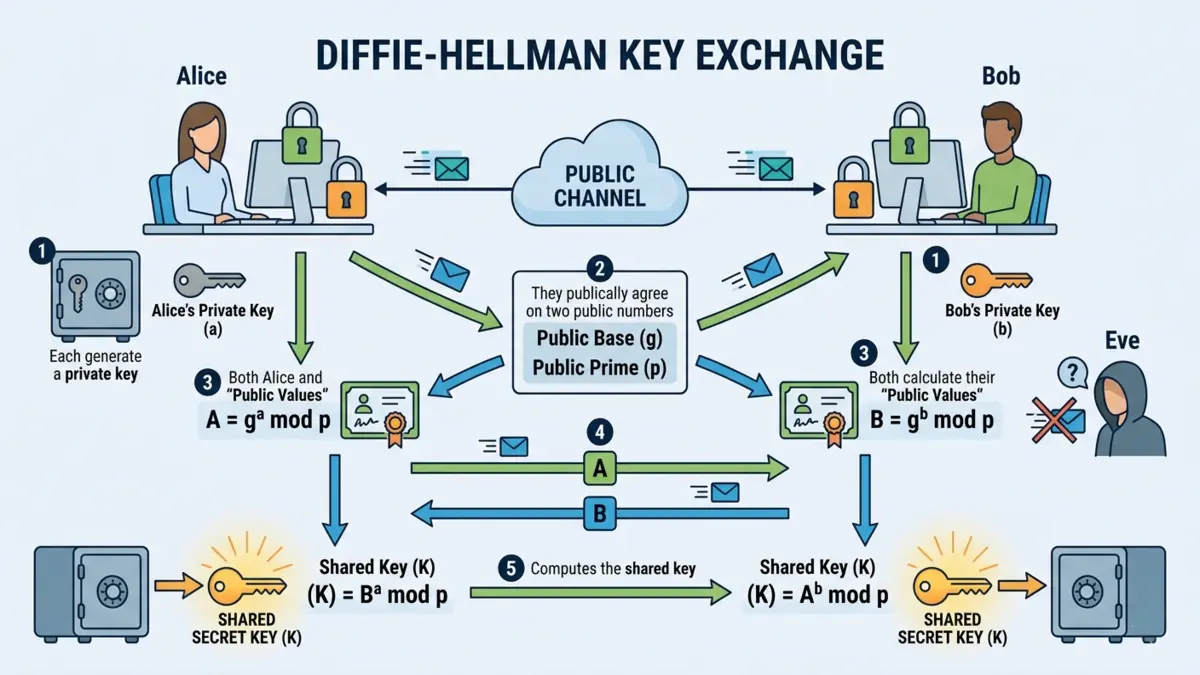
How Does the Hellman Key Exchange Work?
At its core, Diffie–Hellman relies on a mathematical principle called the discrete logarithm problem.
The process sounds complicated, but the idea is surprisingly elegant.
Step 1: Public Parameters Are Shared
Two numbers are chosen publicly:
- A large prime number:
- A generator number:
These values are not secret.
Example:


Step 2: Each User Creates a Private Key
Alice chooses:

Bob chooses:

These numbers remain secret.
Step 3: Public Keys Are Generated
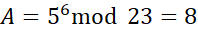
Alice computes:
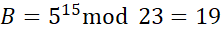
Bob computes:
Using the example values:
Alice sends:
Bob sends:
These public keys are exchanged openly.
Step 4: Both Generate the Same Shared Secret
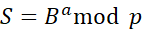
Alice calculates:
Bob calculates:
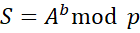
Both arrive at the identical secret value:

An attacker sees:
But cannot practically determine the secret private keys or
.
That computational difficulty is what secures the protocol.
Why is Diffie–Hellman considered secure?
Security depends on one critical asymmetry:
- Modular exponentiation is computationally easy
- Reversing it (discrete logarithms) is extremely hard
For sufficiently large numbers:
- Generating keys takes milliseconds
- Cracking them could take billions of years
Modern implementations use:
- 2048-bit keys
- 3072-bit keys
- Elliptic Curve variants
These sizes make brute-force attacks computationally infeasible with classical computers.
What Is the Difference Between RSA and the Hellman Key Exchange?
People often confuse RSA with Diffie–Hellman because both are public-key cryptography systems.
However, they solve different problems.
| Feature | Diffie–Hellman | RSA |
| Primary Purpose | Key exchange | Encryption & signatures |
| Security Basis | Discrete logarithm problem | Integer factorization |
| Direct Encryption | No | Yes |
| Forward Secrecy | Excellent | Limited in older setups |
| Modern TLS Usage | Extremely common | Declining |
Modern internet security increasingly favors:
- ECDHE (Elliptic Curve Diffie–Hellman Ephemeral)
- Over traditional RSA handshakes
Because ECDHE provides Perfect Forward Secrecy (PFS).
What Is Perfect Forward Secrecy?
Perfect Forward Secrecy means:
- Even if a server’s private key is stolen later
- Past encrypted sessions remain secure
This matters enormously.
Without forward secrecy:
- Attackers could record encrypted traffic today
- Decrypt it years later if they obtain the key
With ephemeral Diffie–Hellman:
- Temporary session keys are destroyed after use
- Old traffic becomes useless to attackers
That is why modern TLS protocols prioritize ECDHE cipher suites.
Where Is the Hellman Key Used Today?
Most internet users interact with Diffie–Hellman daily without realizing it.
HTTPS and TLS
When you visit a secure website:
- Your browser negotiates encryption keys
- Often using ECDHE
- Before any sensitive data is transmitted
This secures:
- Passwords
- Payment information
- Cookies
- Session tokens
VPN Protocols
Protocols like:
- OpenVPN
- IKEv2/IPsec
- WireGuard
Use Diffie–Hellman or elliptic-curve variants to establish secure tunnels.
Secure Messaging Apps
Apps such as:
- Signal
- Telegram
Depend on advanced key exchange systems derived from Diffie–Hellman concepts.
Signal’s famous Double Ratchet protocol combines:
- Diffie–Hellman exchanges
- Symmetric encryption
- Frequent key rotation
To achieve end-to-end encryption.
SSH Connections
When administrators securely connect to Linux servers using SSH:
- Diffie–Hellman algorithms often negotiate session keys
This protects:
- Remote terminal sessions
- File transfers
- Administrative credentials
What Is Elliptic Curve Diffie–Hellman (ECDH)?
Traditional Diffie–Hellman uses modular arithmetic with large primes.
ECDH instead uses:
- Elliptic curve mathematics
- Smaller key sizes
- Faster computations
Advantages include:
- Better performance
- Lower bandwidth usage
- Stronger security per bit
For example:
- A 256-bit elliptic curve key can offer security comparable to a 3072-bit RSA key.
That efficiency matters for:
- Smartphones
- IoT devices
- Embedded systems
- Cloud-scale infrastructure
Can the Hellman Key Exchange Be Hacked?
Not directly, if implemented correctly.
But vulnerability often emerges from poor implementation rather than broken mathematics.
Common Risks
Weak Prime Numbers
Using predictable or reused parameters weakens security.
Man-in-the-Middle Attacks
Classic Diffie–Hellman alone does not authenticate participants.
An attacker could intercept communications and establish separate keys with each side.
This is why protocols combine Diffie–Hellman with:
- Digital certificates
- PKI systems
- Authentication layers
Logjam Attack
Researchers discovered that weak export-grade cryptography enabled attacks against certain TLS implementations.
This pushed the industry toward:
- Stronger key sizes
- Safer TLS defaults
- Better cryptographic hygiene
Is Quantum Computing a Threat to Diffie–Hellman?
Yes, potentially.
Quantum algorithms such as Shor’s Algorithm could theoretically solve discrete logarithm problems efficiently.
That would break:
- Traditional Diffie–Hellman
- RSA
- ECC systems
However:
- Large-scale fault-tolerant quantum computers do not yet exist
- Post-quantum cryptography standards are already being developed
Organizations, including the National Institute of Standards and Technology, are actively standardizing quantum-resistant algorithms.
The future is likely to involve:
- Hybrid cryptographic systems
- Combining Diffie–Hellman with post-quantum algorithms
Why the Hellman Key Still Matters in 2026
Despite being nearly 50 years old, Diffie–Hellman remains foundational because it solves a timeless problem:
How do strangers establish trust securely?
Few inventions in computer science have had such an enduring influence.
Its principles shaped:
- Public-key cryptography
- Internet security protocols
- Secure cloud infrastructure
- Zero-trust architecture
- End-to-end encryption
Even newer cryptographic systems often build upon concepts introduced by Diffie and Hellman.
FAQs
1. Is the Hellman key the same as Diffie–Hellman?
Yes. “Hellman key” usually refers to the Diffie–Hellman key exchange protocol created by Whitfield Diffie and Martin Hellman.
2. Does Diffie–Hellman encrypt data?
Not directly.
It creates a shared secret key that is later used with symmetric encryption algorithms like:
AES
ChaCha20
3. Why is Diffie–Hellman better than sending a password?
Because the secret key is never transmitted across the network.
Even if attackers monitor all traffic, they cannot feasibly derive the shared secret.
4. Is Diffie–Hellman still used?
Absolutely.
Modern internet encryption heavily relies on:
ECDHE
TLS handshakes
VPN protocols
Secure messaging systems
Final Thoughts
The brilliance of the Hellman key exchange lies in its paradoxical simplicity: two parties can create privacy in full public view.
That idea transformed cryptography from a niche military discipline into the backbone of global digital communication.
Every secure website, encrypted app, and protected remote connection owes something to the mathematical insight introduced by Diffie and Hellman in the 1970s.
-

 GENERAL11 months ago
GENERAL11 months agoChristofle – For Those Who Dream of Family Heirloom Silver
-

 SPORTS1 year ago
SPORTS1 year agoDiscover the World of Football with Streameast: Watch Your Favorite Leagues and Tournaments
-

 GENERAL4 months ago
GENERAL4 months agoUncovering the World of кинокрадко: The Dark Side of Film Piracy
-

 GENERAL2 months ago
GENERAL2 months agoATFBooru: Anime, Gaming, and Subculture Imageboard